Phishing remains one of the top cyberthreats to businesses today. To combat such attacks, Microsoft has armed Microsoft 365 Defender with powerful cybersecurity features. Let’s take a look at some of them. 1. Anti-phishing The most dangerous types of phishing scams involve emails that are disguised to appear like it’s from an entity.
How does Microsoft 365 Defender fight phishing?
5 Simple tips for a successful web conversion
Ignore these outdated disaster recovery myths
New enhancements that Windows 11 has to offer
Steps to implementing a proactive cybersecurity strategy
How to get the best out of Microsoft Word
How much internet bandwidth do remote workers need?

While working from home, you need to have the right amount of resources and support to be productive. You need a functioning computer and sufficient internet bandwidth. But chances are, you’re not aware of the minimum internet bandwidth requirements needed to be fully productive while working away from the office.
Top tips when selecting an MSP for your business

Technology underpins nearly every aspect of modern business processes. Managing it, however, can be complex and tedious. This is where managed IT services providers (MSPs) can help. Whether your company needs software solutions, network infrastructure management services, or cloud technology, MSPs can provide all this and more.
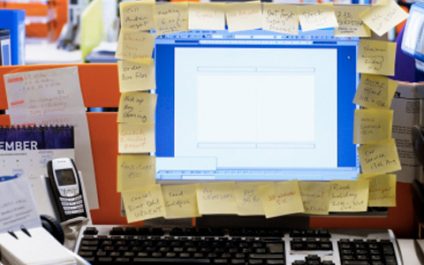
How to declutter your desktop effectively
How to keep your email account safe

Many businesses use email to send and receive sensitive information, making it an attractive target for cyberattacks. To reduce your exposure to cyberthreats, implement the following email security measures. Use separate email accounts Most people use a single email account for all their online tasks.
- 1
- 2